Solutions
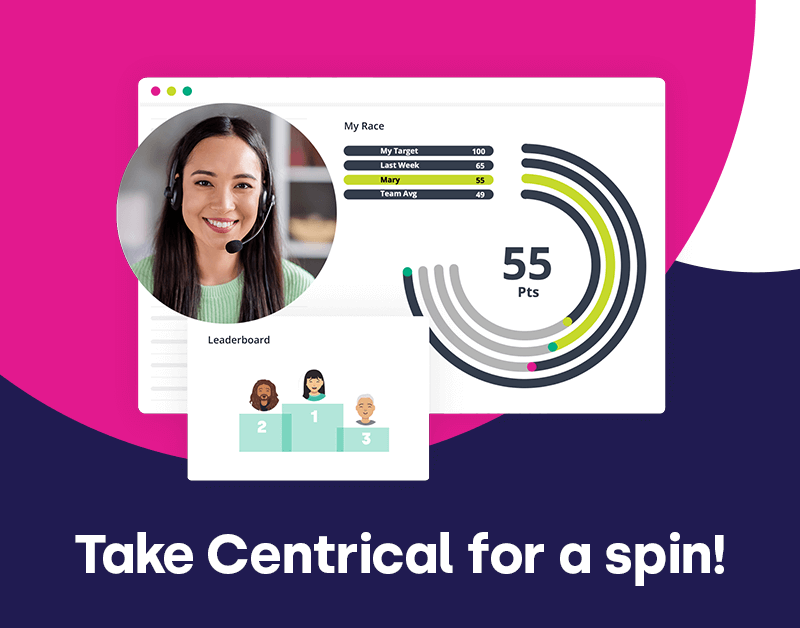
Centrical’s suite of software solutions helps leading enterprises improve frontline employee performance.
Platform
Department
Industry
Use Case
Company
Resource Center
Back
Solutions
Platform
Department
Company
- Solutions
- Platform
- Gamification
Engage and motivate your frontline teams
- MegAI
Improve performance with an AI-powered digital coach
- Quality Assurance
Deliver world class CX with dynamic, actionable quality evaluations
- Performance Management
Boost performance with personalized, actionable goals
- Coaching
Nurture employee success with the power of AI
- Voice of Employee
Listen and respond to your frontline, continuously
- Microlearning
Drive productivity with performance-driven learning that sticks
- Gamification
- Department
- Industry
- BPO
Drive agent efficiency, deliver client results
- Technology
Keep tech teams motivated and proficient on products and services while exceeding targets
- Finance
Maintain compliance while building customer happiness and loyalty
- Energy
Enlighten energy teams to boost engagement
- Insurance
Engage, develop, and retain your agents while driving better CX
- Hospitality
Improve the employee experience for your reservations and service desk agents
- BPO
- Use Case
- Platform
- Company
- Pricing
- Resources
- Request Demo
- See a Preview
- View Product Tour






 Madeleine Freind
Madeleine Freind
 Natalie Roth
Natalie Roth Linat Mart
Linat Mart











 Doron Neumann
Doron Neumann Gal Rimon
Gal Rimon Daphne Saragosti
Daphne Saragosti Ella Davidson
Ella Davidson Ariel Herman
Ariel Herman Ronen Botzer
Ronen Botzer